Why would Internet Archive have people’s passwords stored?
The bad news is that you have an Internet Archive account, your username and email could well have been captured by the site’s attackers.
Oh so it’s not a problem for anyone without an Internet Archive login?
Oh so it’s not a problem for anyone without an Internet Archive login?
TIL, that you can have an account for the Internet Archive. I guess I use it differently than most people, but it’s often a one-and-done use case when I visit.
You need an account to upload stuff. The Internet Archive isn’t just archiving websites, you can also upload book scans to them, rips of old floppies and discs for old software, even old TV shows and movies. For example, the entirety of the Computer Chronicles series is available for download there.
Wow. That’s cool.
If you want to borrow a digitized bok from their library you need a login.
Because of the nature of the Internet archive, I too was wondering this.
Yes, as with all password leaks, they only leak the passwords they have.
I guess I get to have a little chuckle over this one. I have terabytes of stuff stored on the archive, but I have no account or password there haha! Pretty neat what one can do with the snapshot feature.
For real though, that sucks for everyone with an account.
You can save snapshots including outlinks if you are logged in… Very useful for me.
I got a whole filesystem going on the archive, no account. Outlinks are almost easy peasy. Just archive a ZIP file that contains an HTML file with your own directory of links.
I never claimed to be a normal archivist, but as long as I can avoid it, I’m not gonna create an account.
Wait really?!
I never really thought about it I guess - I’ve got a bunch of stuff I’m archiving locally that I always felt like it’d be a shame if it disappeared. Would be nice to have a real place for it.
My method is a bit cumbersome, but basically you upload the file to one of the temporary file sharing sites, then get and copy the full download link, but don’t actually download it.
Take the copied full link, and use the archive’s snapshot feature. Your mileage may vary, not all temp sharing sites allow archiving.
I would if I could actually log in. It’s getting ddos’d.
I managed to get in and change mine last night. So you just have to keep hammering that refresh button until you overcome whoever this asshole is that’s DOSing the site. Maybe even do it on several computers, and write a script to help.
Edit: Joke, don’t do.
You’re contributing to the DDoS attack. Just wait, if your password is good enough and not in use elsewhere it should take a while to crack the hash.
Pretty sure that was a joke >.>
This might be a silly question but it might not - if let’s say 5 (or even 50) people use the same username and password in multiple sites, and they have another site’s leak. Would they be able to easily crack the hash?
They will start a dictionary attack on the most common passwords and check their hashes against the stolen database. The speed depends on whether the password hashes obtained are salted in a known method (or not at all). If so, they can perform the dictionary search or brute force locally and VERY quickly.
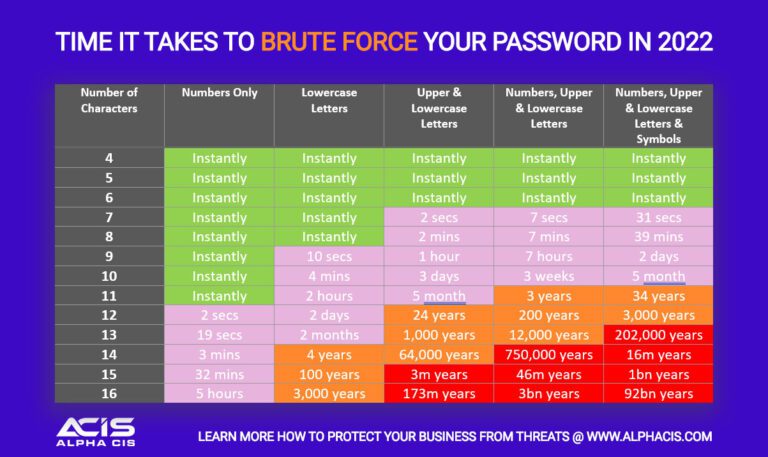
Take these charts with a grain of salt, they always depend on the attacker’s computing power. My password was generated with a password manager and it will take millenia to crack with a reasonable number of modern GPUs so I’ll be able to change it in time.
If the method is not known, they will need to go through the servers, which have rate limits.
The passwords are probably hashed with usernames so they can only attack one person at once but of course, once they have the plaintext password, they can use it anywhere else the user reused it or a variation of it.
If the password hashes aren’t salted they can be cracked with a rainbow table - every password up to (whatever length the rainbow tables go up to now - 10 chars?) is easily cracked in seconds
I expect Internet archive salts their password hashes.
It doesn’t matter if the salting method is known, all salting methods are known and it’s easy to see what salt a password is hashed with as you need to know so you can hash a received password the same way for validation
Not a silly question! The answer is technically yes, but not really.
Considering there are still sites that store plaintext passwords, there has to be some that just hash it and call it a day. For those, once you crack the hash, you know everyone with the same hash has the same password. Any real site does some more complex stuff to “personalise” each hashed password.
The real issue is when you reuse the password and it gets cracked once, people will try that with your email for other leaks and live sites. If a lot of people use the same password (like “password123”), they’re likely to try it as one of the first guesses to crack any new leaks.
I’m oversimplifying my already oversimplified knowledge of basic cryptography, but it’s a really interesting topic!
I was joking. Don’t do this.
I can’t change the password because the site is still down. Although my password is randomly generated and different to any of my others.
Update 2 days later: Yep, I’m one of the 31M affected users. Still waiting for the site to go up so I can change the password. Check if you’ve been affected on https://haveibeenpwned.com/
The idea is to change your passwords on other sites if they shared the same password (which is why you shouldn’t do this).
The real advice is to use a password manager to generate random passwords and store them for you, so no two passwords are the same, and the only password you need to remember is the one to unlock the password manager
I use keePass as it’s open source and available on all operating systems. Also you can move the camel case in your head to make it keepAss.