

common aegis W


common aegis W
you can use something like smspool.net to verify the account with a one time use #. then google will allow you to link an authenticator app to the account. removing the # from the account afterwards does not remove the TOTP code either.
yeah that seems to be from all the way in 2021 unfortunately. you may be stuck with the browser version :(
you can try looking it up on plexus to see if others have had success using that app
I got my 7a referbished for 350. the nothing phone is cool IMO but probably not going to have good support rn for nieche stuff. lineage & divest not having working versions for the phone raises red flags personaly.
if you are anti pixel & $500 is in your price range maybe take a look at the fairphone 4?
honestly I would personaly look into a used option just for pricing reasons. I think the 8 offered additional security benefits though. It may be a while until the 9 drops but that would also be an option.
if you want to degoogle the only way to run some apps without unprivileged code (GMS/microG) is to use grapheneos & its sandbox compatibility layer. this is unfortunately only available on the pixels.
I also worry you won’t be able to use some of the customization options that the nothing phone 2 offers with its hardware when using a custom ROM. if thats something u care about.
I have the pixel 7a & have had essentialy no issues with anything for what that’s worth.


session doesnt have perfect forward secrecy. they removed it from signals protocol to make it more easily compatible with their onion routing/crypto network. makes it one of the easiest apps to be “backdoored” if any keys were to be compromised.
there’s a foss flavor on the Fdroid repo that doesnt have any trackers I believe


oh I see interesting. seems like blatant malpractice to me. good luck on your paper o7


thank you 🙏
I meant that if you look at the “purpose” section of each cookie the ones that are older than 180 days are the only ones that dont mention advertising. thinking they may be related to the “nessecary” or “required” cookies that some websites have. I would presume they have their own or altered version of the other cookies policies since they have different purposes.
apologies, I worded that poorly before.


while I am by no means an expert on this, my gut tells me that this is probably something to do with “nessecary” cookies vs advertising & tracking cookies. its a common loophole for other policies so I wouldnt be surprised if they had some way of circumventing the normal limitations for tracking because of “fraud protection” or the likes.
looking at the cookie descriptors, all of the 1825 day cookies are used to “store &/or access information on device refreshes”. the shorter cookies are the only ones that also mention “measuring advertising & content performance”.
ahhh I see what you mean.
your thoughts on spacing out your connections & isolating is smart. unfortunately if you connect from the same device & browser any government agency or dedicated company with a big enough dataset (google, meta, etc.) would still be able to link you regardless of you IP by browser fingerprint alone. this does make YouTube more specifically being linked to your exact browser fingerprint porblamatic in a high stakes situation. As it, as you said is linked to your identity.
for lower level tracking changing IP regularly is effective. however, instead of switching to your local IP it would be more privacy conscious to just switch to a different VPN server.
unfortunately if you are genuinely worried about government level surveillance or the likes u enter into territory where VPNs often no longer cut it (or at least can’t truly be trusted too) as they are centralized & can be forced to make exceptions for law enforcement. traffic analysis is also easier, which makes time correlation deanonimization a more realistic risk when talking about government agencies specifically.
the tor + vpn debate is one that lots of people argue & is excedingly complicated. tor is generally more than enough, unless you are wanted by INTERPOL haha. if you are genuinely worried about suppressive government or world powers targeting you look further into tor, & do not connect directly to your ISP at all as that data is essentially up for grabs to local authorities (depending on locale).
for you specifically I would consider doing your more sensitive tasks in the tor browser without the VPN & then having your normal browser always on the VPN so they would be more difficult to correlate. anything torrent related is low enough stakes that I would imagine just about any proxy would suffice. hope this was helpful 🙏.
tldr; no, if you trust your vpn more than your ISP always use it, as any hit to fingerprinting is menial.
it really can’t hurt much to always be using it. any fingerprinting metric it would give is outweighed by the hiding of your IP behind the proxy. this is the #1 unique identifier that is tied back to people/locations.
the other fingerprinting metrics also are still exposed anyway & could probably be linked back to “you” regardless of your IP changing if they wanted too.
if you are worried about fingerprinting look into some projects like mullvad, librewolf, or even tor. clearing cookies on quit &/or having a separate browser for permenant logins/tokens to live in is also a good mitigation technique.
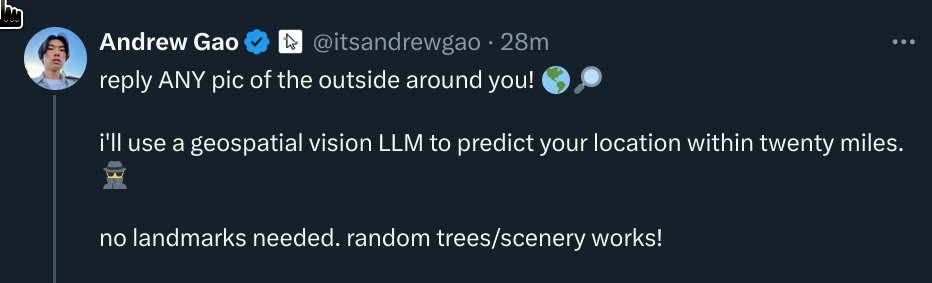
important second frame for context!
& no it isnt. quite sure twitter broke link previews a long time ago alongside guest accounts.
this is extremely scary if true. are these algorithms obtainable by every day people? do they work only in heavily photographed areas or do they infer based on things like climate, foliage, etc? I would love some documentation on these tools if anyone has any.


outside of sandboxing/limiting android auto via grapheneos good luck.
if you just want audio & your car doesnt support Bluetooth you could use an adapter to take it from Bluetooth to 3.5 aux. if your car is so fancy it doesn’t have aux input you can get a Bluetooth to FM radio adapter that will take over one the channels in your car as well.
scrambled exif is really practical & easy to use. it has been a player for a while now where as metadata remover seems newer & possibly less trustworthy/vetted because of it.
it also doesnt seem to add much new functionality from scrambled exif besides viewing data in app.
I personally use image toolbox which allows you to select what specific exif tags you would like to remove. however, I wouldnt put any more trust in its accuracy or comprehensiveness than any other adjacent app as they realistically all probably work very similarly.
if its imperitive you don’t leak any exif data I would recommend checking that in an external & more trusted app anyway. something like aves or a similar gallery that will lay out all all metadata tied to an image.


quite sure this isn’t implemented at the moment unfortunately. I have a similar setup & similar issue but haven’t been able to resolve it.
it may be possibly to set up some kind of dual setup using unified push to receive notifications on both profiles, but I haven’t been able to find a tool to do so & am doubtful after looking at the way unified push works.
self hosting is the only way to guarantee logs arent shared.
however it also means that your server address only pulls requests for things YOU look at, not the whole pool of people using the server. imo this is a bad trade off as it would allow the services to track my browsing easily anyway.
personally I would recommend looking at libredirect with a large # of frontend instances selcted & a vpn/tor. these websites normally work without javascript, so assuming you have a privacy focused browser your IP is the only tracking metric they really have. spreading your requests out over different servers whilst using a proxy would make this really difficult to correlate as it would require that mutliple instance operators were malicious & collaborating.